By Joy Chik, President, Identity & Network Access
A year ago when we announced the Microsoft Entra product family, we asked what the world could achieve if we had trust in every digital experience and interaction.1 This question inspired us to offer a vision for securing the millions and millions of connections that happen every second between people, machines, apps, and devices that access and share data.
Protecting identities and access is critical. As our work and lives become increasingly digital, cyberattacks are becoming more frequent and more sophisticated, affecting organizations of every size, in every industry, and in every part of the world. In the last 12 months, we saw an average of more than 4,000 password attacks per second, an almost threefold increase from the 1,287 attacks per second we saw the previous year.2 We’re also seeing far more sophisticated attacks, including ones that manage to evade critical defenses, such as multifactor authentication, to steal access tokens, impersonate a rightful user, and gain access to critical data.
To help organizations protect their ever-evolving digital estates, we’ve been expanding beyond managing directories and authenticating users to securing and governing access for any identity to any app or resource. Today, we’re thrilled to announce the next milestone in our vision of making it easy to secure access with two new products: Microsoft Entra Internet Access and Microsoft Entra Private Access. We’re adding these capabilities to help organizations instill trust, not only in their digital experiences and services but in every digital interaction that powers them.
Secure access to any app or resource, from anywhere
Flexible work arrangements and the resulting increase in cloud workloads are straining traditional corporate networks and legacy network security approaches. Using VPNs to backhaul traffic to the legacy network security stack weakens security posture and damages the user experience while using siloed solutions and access policies leaves security gaps.
Microsoft Entra Internet Access is an identity-centric Secure Web Gateway that protects access to internet, software as a service (SaaS), and Microsoft 365 apps and resources. It extends Conditional Access policies with network conditions to protect against malicious internet traffic and other threats from the open internet. For Microsoft 365 environments, it enables best-in-class security and visibility, along with faster and more seamless access to Microsoft 365 apps, so you can boost productivity for any user, anywhere. Microsoft 365 scenarios in Microsoft Entra Internet Access are in preview today, and you can sign up for the preview of capabilities for all internet traffic and SaaS apps and resources that will be available later this year.
Microsoft Entra Private Access is an identity-centric Zero Trust Network Access that secures access to private apps and resources. Now any user, wherever they are, can quickly and easily connect to private apps—across hybrid and multicloud environments, private networks, and data centers—from any device and any network. Now in preview, Microsoft Entra Private Access reduces operational complexity and cost by replacing legacy VPNs and offers more granular security. You can apply Conditional Access to individual applications, and enforce multifactor authentication, device compliance, and other controls to any legacy application without changing those applications.
Together, Internet Access and Private Access, coupled with Microsoft Defender for Cloud Apps, our SaaS security-focused cloud access security broker, comprise Microsoft’s Security Service Edge (SSE) solution. We’ll continue to evolve our SSE solution as an open platform that delivers the flexibility of choice between solutions from Microsoft and our partners. Pricing for Microsoft Entra Internet Access and Microsoft Entra Private Access will be available when those products reach general availability.
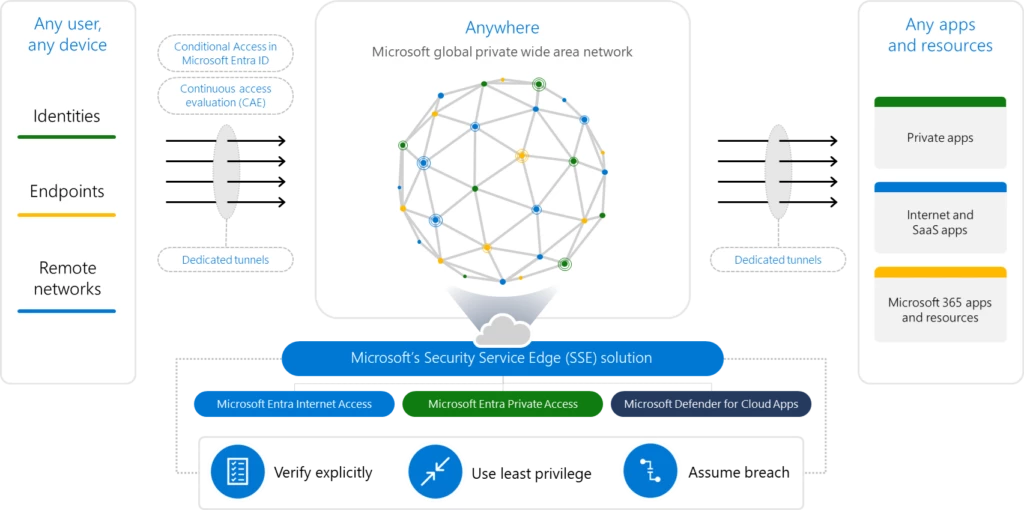
Figure 1. Microsoft’s Security Service Edge (SSE) solution.
Neither identity nor network security alone can protect the breadth of access points and scenarios that modern organizations require. That’s why, as cyberattacks get more sophisticated, we’re adding identity-centric network access to our cloud identity solutions. We’re converging controls for identity and network access so you can create unified Conditional Access policies that extend all protections and governance to all identities and resources. With a single place to safeguard and verify identities, manage permissions, and enforce intelligent access policies, protecting your digital estate has never been easier.
Microsoft Azure Active Directory is becoming Microsoft Entra ID
When we introduced Microsoft Entra in May of 2022, it included three products: Microsoft Azure Active Directory (Azure AD), Microsoft Entra Permissions Management, and Microsoft Entra Verified ID.1 We later expanded the Microsoft Entra family with Microsoft Entra ID Governance and Microsoft Entra Workload ID.3 Today, Microsoft Entra protects any identity and secures access to any resource—on-premises, across clouds, and anywhere in between—with a product family that unifies multicloud identity and network access solutions.
To simplify our product naming and unify our product family, we’re changing the name of Azure AD to Microsoft Entra ID. Capabilities and licensing plans, sign-in URLs, and APIs remain unchanged, and all existing deployments, configurations, and integrations will continue to work as before. Starting today, you’ll see notifications in the administrator portal, on our websites, in documentation, and in other places where you may interact with Azure AD. We’ll complete the name change from Azure AD to Microsoft Entra ID by the end of 2023. No action is needed from you.
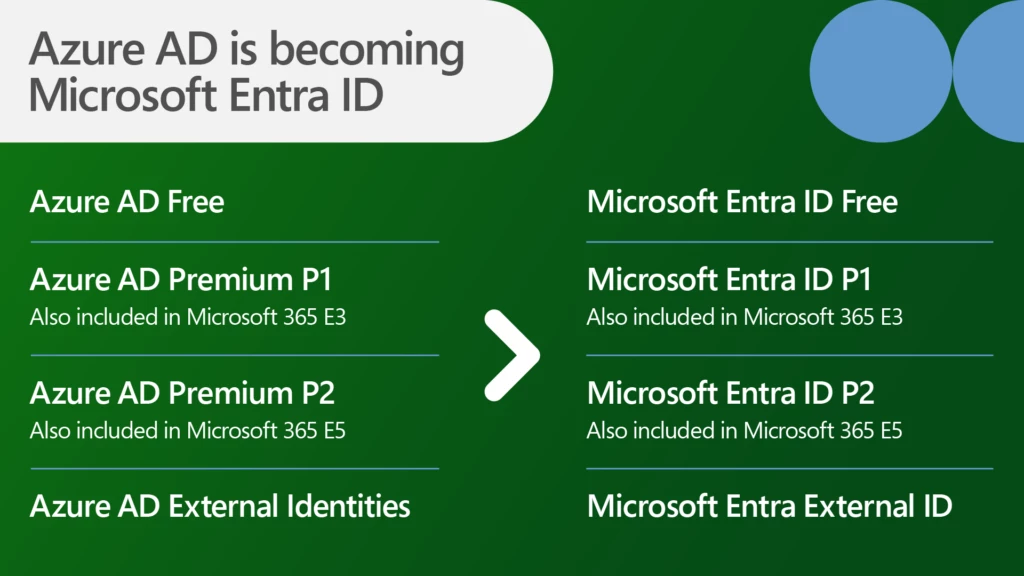
Figure 2. With the name change to Microsoft Entra ID, the standalone license names are changing. Azure AD Free becomes Microsoft Entra ID Free. Azure AD Premium P1 becomes Microsoft Entra ID P1. Azure AD Premium P2 becomes Microsoft Entra ID P2. And our product for customer identities, Azure AD External Identities, becomes Microsoft Entra External ID. SKU and service plan name changes take effect on October 1, 2023.
More innovations in Microsoft Entra
Today we’d also like to highlight other innovations in the Microsoft Entra portfolio that strengthen defenses against attackers who are becoming more adept at exploiting identity-related vulnerabilities such as weak credentials, misconfigurations, and excessive access permissions.
Prevent identity takeover in real time
Several exciting changes to Microsoft Entra ID Protection (currently Azure AD Identity Protection) help IT and identity practitioners prevent account compromise. Instead of reactively revoking access based on stale data, ID Protection uses the power of advanced machine learning to identify sign-in anomalies and anomalous user behavior and then block, challenge, or limit access in real time. For example, it may trigger a risk-based Conditional Access policy that requires high-assurance and phishing-resistant authentication methods for accessing sensitive resources.
A new dashboard demonstrates the impact of the identity protections that organizations deploy with a comprehensive snapshot of prevented identity attacks and the most common attack patterns. On the dashboard, you can view simple metric cards and attack graphs that show risk origins, security posture over time, types of current attacks, as well as recommendations based on risk exposure, while highlighting the business impact of enforced controls. With these insights, you can further investigate your organization’s security posture in additional tools and applications for enhanced recommendations.
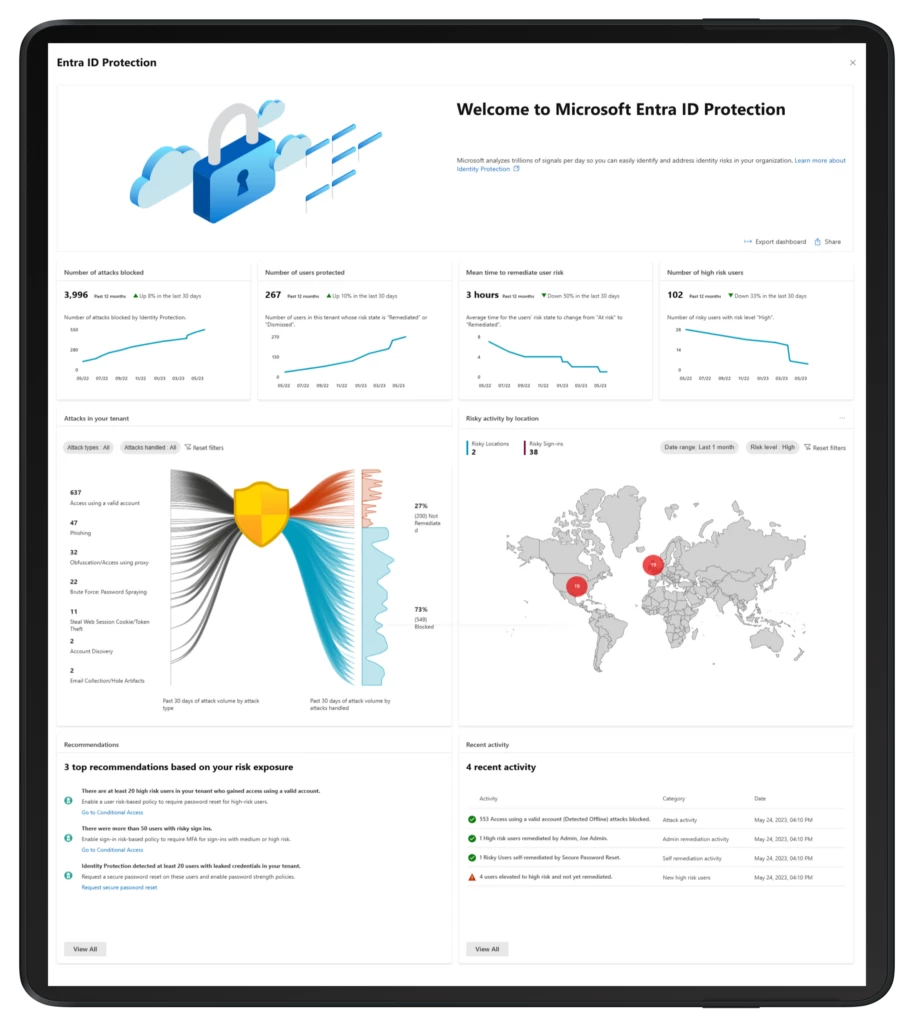
Figure 3. New Microsoft Entra ID Protection dashboard.
Automate access governance
An important part of securing access for any identity to any app is ensuring that only the right identities have the right access at the right time. Some organizations only realize they need to take this approach when they fail a security audit. Microsoft Entra ID Governance, now generally available, is a complete identity governance solution that helps you comply with organizational and regulatory security requirements while increasing employee productivity through real-time, self-service, and workflow-based app entitlements.4
ID Governance automates the employee identity lifecycle to reduce manual work for IT and provides machine learning-based insights about identities and app entitlements. Because it’s cloud-delivered, it scales to complex cloud and hybrid environments, unlike traditional on-premises identity governance point solutions. It supports cloud and on-premises apps from any provider, as well as custom-built apps hosted in the public cloud or on-premises. Our global system integrator partners—including Edgile, a Wipro company, EY, KPMG, and PwC—started helping with the planning and deployment of ID Governance on July 1, 2023.
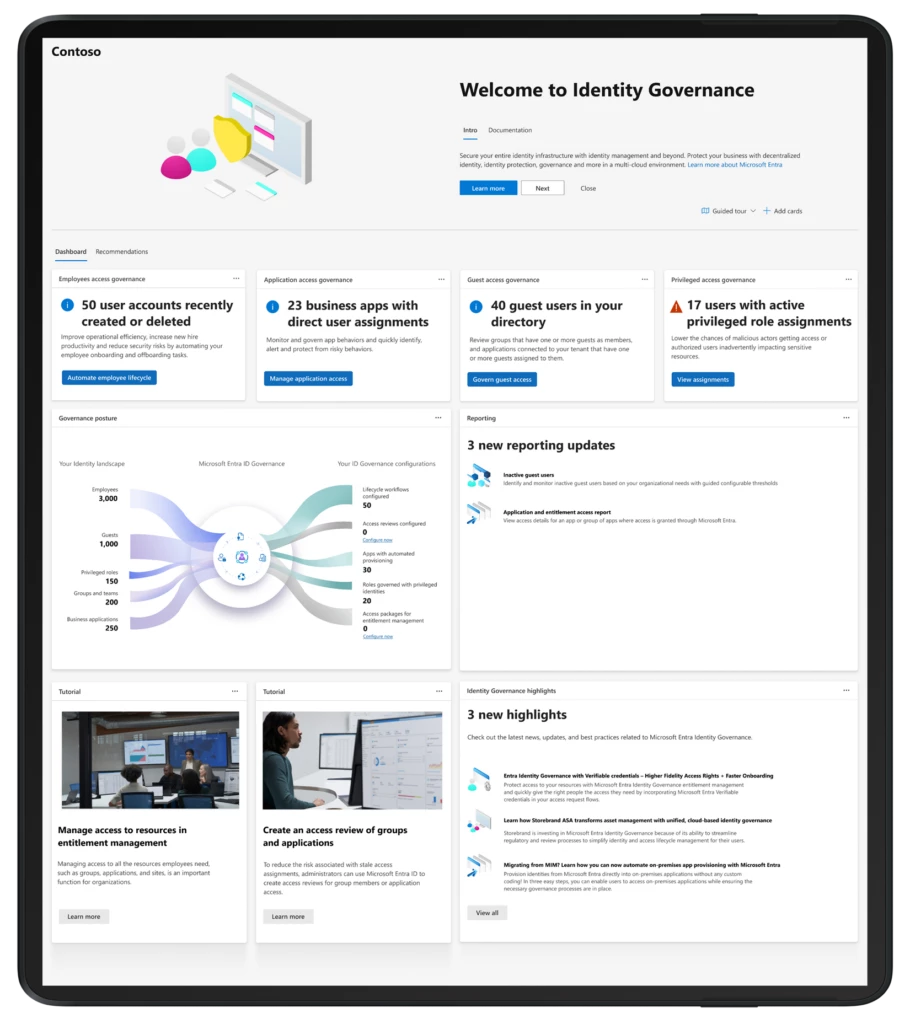
Figure 4. New Microsoft Entra ID Governance dashboard.
Personalize and secure access to any application for customers and partners
As we announced at Microsoft Build 2023, new developer-centric capabilities in Microsoft Entra External ID are now in preview. External ID is an integrated identity solution for external users, including customers, patients, citizens, guests, partners, and suppliers. It offers rich customization options, Conditional Access, identity protection, and support for social identity providers. Using our comprehensive developer tools, even those developers who have little to no identity experience can create personalized sign-in and sign-up experiences for their applications within minutes.
Simplify identity verification with Microsoft Entra Verified ID
Since we announced the general availability of Microsoft Entra Verified ID last summer, organizations around the world have been reinventing business processes, such as new employee onboarding, around this new, simpler way of verifying someone’s identity.5 For example, we recently announced that millions of LinkedIn members will be able to verify their place of work using a Verified ID credential.6 At the 2023 Microsoft Build event, we launched the Microsoft Entra Verified ID SDK so that developers can quickly add a secure digital wallet to any mobile application. The app can then store and verify a wide range of digital ID cards.
Microsoft Entra: Secure access for a connected world
You can see our expanded Microsoft Entra product family in Figure 5. Visit the Microsoft Entra website to learn more.
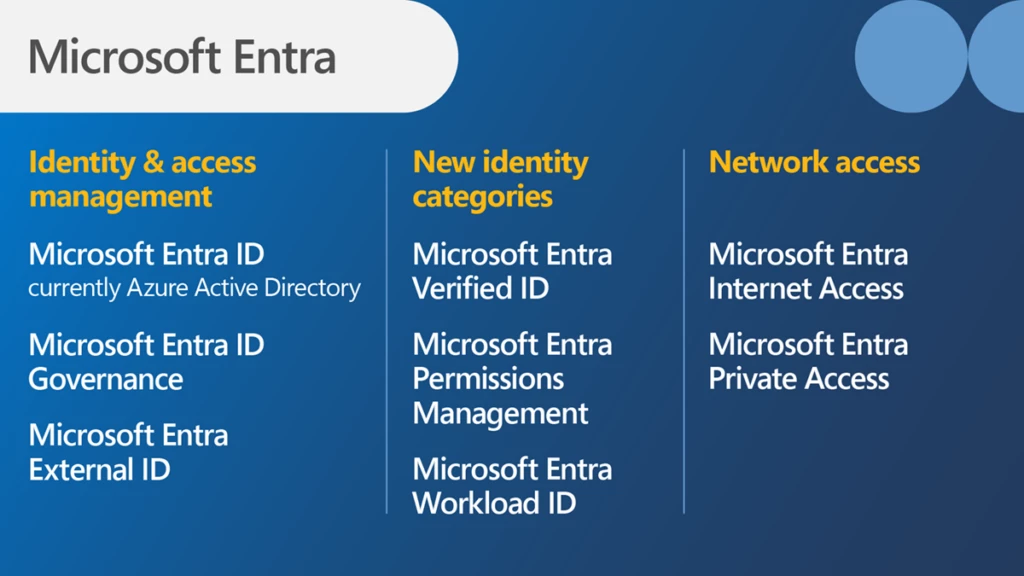
Figure 5. The Microsoft Entra family of identity and network access products.
We’re committed to building a more secure world for all and making life harder for threat actors, easier for admins, and more secure for every user. As part of that commitment, we’ll keep expanding Microsoft Entra to provide the broadest possible coverage along with a flexible and agile model where people, organizations, apps, and even smart things can confidently make real-time access decisions.
Encourage your technical teams to dive deeper into these announcements by attending the Tech Accelerator event on July 20, 2023, on the Microsoft Tech Community.
Microsoft Entra
Meet the family of multicloud identity and access products.

Learn more
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and Twitter (@MSFTSecurity) for the latest news and updates on cybersecurity.
1Secure access for a connected world—meet Microsoft Entra, Joy Chik and Vasu Jakkal. May 31, 2022.
2Microsoft internal data.
3Do more with less—Discover the latest Microsoft Entra innovations, Joy Chik. October 19, 2022.
4Microsoft Entra ID Governance is generally available, Joseph Dadzie. June 7, 2023.
5Microsoft Entra Verified ID now generally available, Ankur Patel. August 8, 2022.
6LinkedIn and Microsoft Entra introduce a new way to verify your workplace, Joy Chik. April 12, 2023.










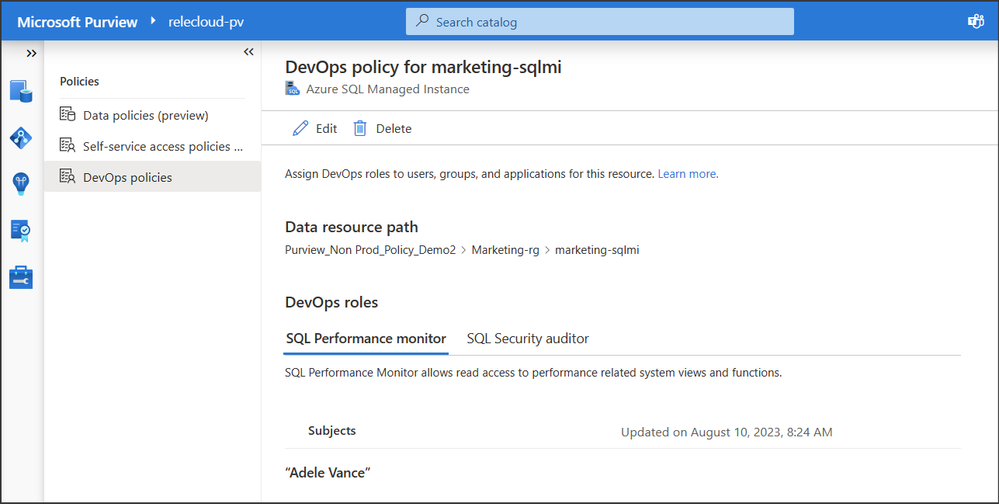 Figure 1: Screenshot of DevOps policy
Figure 1: Screenshot of DevOps policy